We used to get emails, "all you data is ours" - from some purported hacker, saying "you" instead of "your".. a dead give-away one was getting spam, phishing, or some other ploy to get you to open the potentially suspect post.
BUT if one IS an international traveler, and is going FROM the United States or INTO the United States, and you have an electronic device, read "Cellphone, Computer, or other recording device", your device is subject to inspection. Meaning the device will be read, the data stored and ANALYZED, including your emails (if stored on the device), all your pictures, music, video's, texts, your contact book (and if you have stored your passwords in plaintext) they are all going to end up in the TSA/HSA/Customs and Border Patrol database.
US Customs and Border Protection is where the offences appear to be happening.
US Customs and Border Protection (CBP) agents are being allowed to search travelers mobile devices without probable cause.
The explanation? Well the traveler may be traveling with State Secrets, or Child Pornography. Therefore they have the right they say, to search without probable cause.
Trawling through data stored locally on a phone or computer is allowed, but anything found solely on the cloud is off limits and that includes your social media accounts. If they get to your cloud account it was through passwords stored in your device. Or if your cloud account was left open and accessible to your device.
CBP has 'legal' authority to conduct border searches extends to all merchandise entering or departing the United States, including information that is physically resident on an electronic device transported by an international traveler.
History - there were only about 4,500 searches in 2015, but in 2016 this jumped to 23,000 searches. CBP maintains that searching travelers phones without probable cause protects against child pornography and threats to national security.
What if you say NO ! -
Anyone entering the country can refuse to hand over passwords to their phones and laptops when asked, but border officials may detain the devices for further examination, and any non-citizens risk being denied entry if they do so.
Automatic Targeting System -
Over 787 million travelers entered the U.S. in 2016 and 2017, 47,400 of whom had their electronic devices subject to a search, including advanced searches.
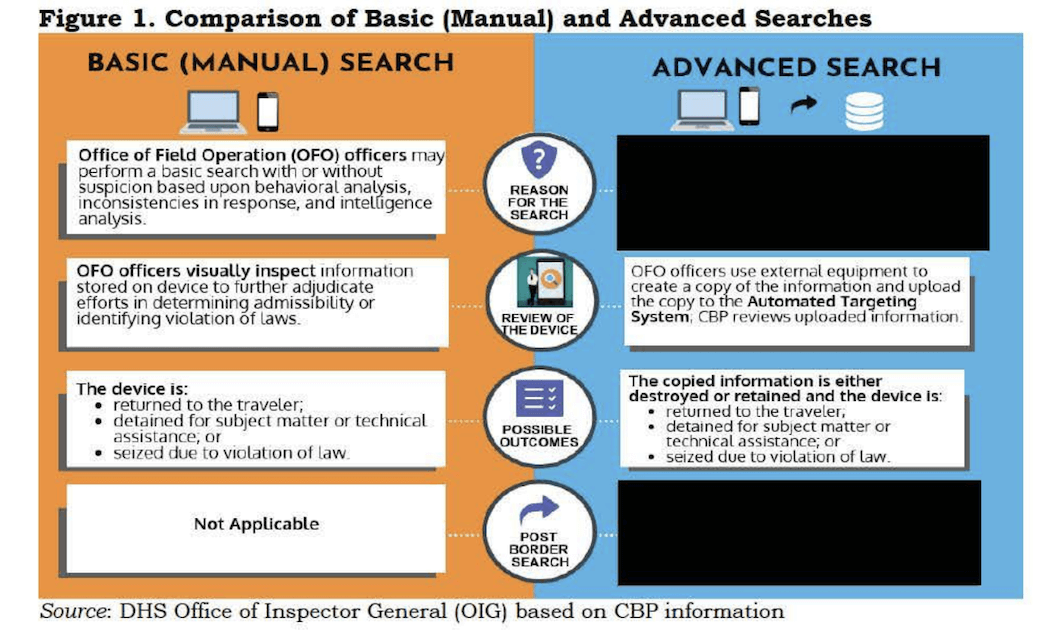
Unlike a basic search, which involves visually checking phones, laptops, etc. without downloading anything, advanced searches consist of downloading data onto USB drives and plugging them into CBPs Automated Targeting System so it can be analyzed.
They are KEEPING the data -
According to an Office of the Inspector General (OIG) report, many customs officials are failing to delete travelers information from these drives following an advanced search.
(As noted by Gizmodo, a lot of the report was redacted, including the reasons why an advanced search takes place and what happens afterwards. Its also noted how U.S. Customs and Border Protection forgot to renew its license for the software it uses to conduct the advanced searches.)[The Office of the Inspector General] physically inspected thumb drives at five ports of entry.
At three of the five ports, we found thumb drives that contained information copied from past advanced searches, meaning the information had not been deleted after the searches were completed.
Based on our physical inspection, as well as the lack of a written policy, it appears [Office of Field Operations] has not universally implemented the requirement to delete copied information, increasing the risk of unauthorized disclosure of travelers data should thumb drives be lost or stolen.
Is the US the only one doing the electronic strip search? No.
New Zealand says they can DEMAND passwords for any electronic device.
https://www.techspot.com/news/69983-...passwords.html
According to an investigative report by New Zealand's 1 news, airport customs officials routinely force up to two travelers each day to give up their electronic devices and passwords for searching.
According to the customs agents, the program is designed to look for smugglers by performing a "digital strip search" on the phones and laptops of travelers.
This does not require a court order, but the agents do claim to adhere to New Zealand's privacy act.
The searches can be quick or much more extensive depending on the level of danger perceived. One traveler was stopped for five hours and claims he was "made to feel like a terrorist" on his way home from Bali. Agents typically just peruse the data looking for any red flags but they have admitted to also copying it and passing it along to the government and police. According to the customs general manager, agents can seize travelers' devices at any moment and they have tools to break some types of encryption if it is encountered.
Since 2015 more than 1,300 people have been stopped and searched at New Zealand's three biggest airports. Of these, just under 300 were actually from New Zealand. Chinese and Taiwanese travelers accounted for 360 searches as well.
If travelers refuse to comply, a bill is currently being considered by parliament to fine them up to $5,000.
- Home
- Forum
- Chat
- Donate
- What's New?
-
Site Links

-
Avalon Library

-
External Sites

- Solari Report | Catherine Austin Fitts
- The Wall Will Fall | Vanessa Beeley
- Unsafe Space | Keri Smith
- Giza Death Star | Joseph P. Farrell
- The Last American Vagabond
- Caitlin Johnstone
- John Pilger
- Voltaire Network
- Suspicious Observers
- Peak Prosperity | Chris Martenson
- Dark Journalist
- The Black Vault
- Global Research | Michael Chossudovsky
- Corbett Report
- Infowars
- Natural News
- Ice Age Farmer
- Dr. Joseph Mercola
- Childrens Health Defense
- Geoengineering Watch | Dane Wigington
- Truthstream Media
- Unlimited Hangout | Whitney Webb
- Wikileaks index
- Vaccine Impact
- Eva Bartlett (In Gaza blog)
- Scott Ritter
- Redacted (Natalie & Clayton Morris)
- Judging Freedom (Andrew Napolitano)
- Alexander Mercouris
- The Duran
- Simplicius The Thinker




 Reply With Quote
Reply With Quote


Bookmarks