.
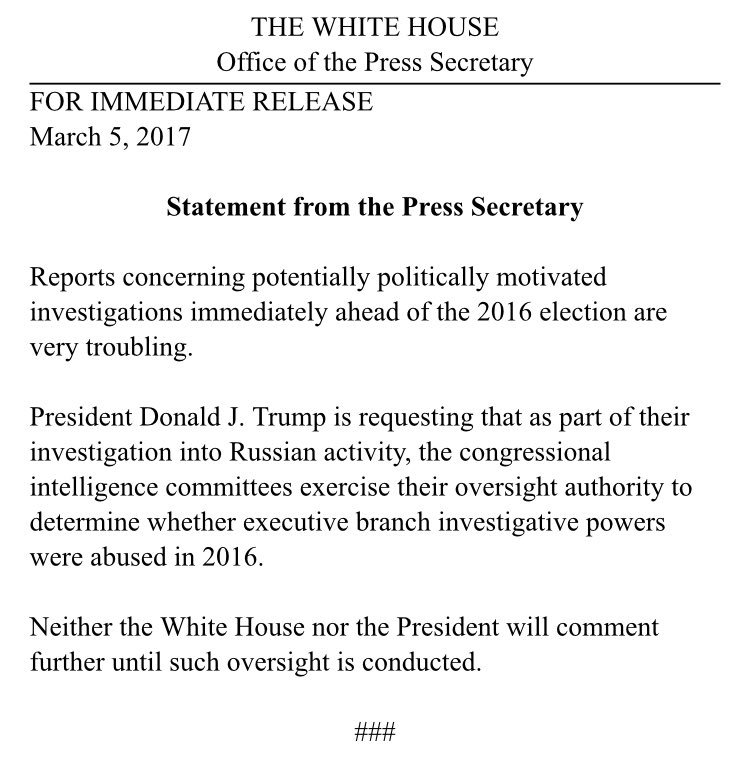
As promised by our DHS insider earlier this week, our FBI insider surfaces with information on #ObamaGate and a Spring Purge. If you heard our interview with Robert David Steele, he also spoke of a Spring Purge. This all falls together like pieces of a puzzle. Below is the latest question and answer by FBI Anon:Q. Thank you for talking with us. What do you think of Trumps allegations against Obama?A. In the worlds of the Carpenters, its only just begunQ. So was Trump wiretapped as our DHS insider and Robert Steele suggestA. Yes.Q. Why?A. Wrong questionQ. Ok, by whom?A. Trump tower was bugged by more than just our IC.Q. WHAT????? Could you elaborate?A. Brits, Israelis. In the fullness of time, much will be revealedQ. Why the Brits?A. The same reason as the Israelis. Trump is a threat to the Deep State. The Deep State is a threat to Trump. Globalists are the populations bee keepers. They harness the energy, they harness the honey. Controlled oppression.Q. So why do you and other insiders leak to us and others?A. Because once in a while, a bat needs to be taken to the bee hive.Q. So you want the bees swarming?A. In a manner of speaking. We leak, so that the people may have a just outrage and demand a just result. The People outnumber the Government 300 to 1. Its a numbers game. We expected high level arrests to happen weeks ago, but discovered the bee keepers had interfered at the highest levels. There is an internal war within our Government, as many know. The Shadow State is like a vampire facing dawn. They do not go easily into sunlit areas.Q. So why did the Israelis bug TrumpA The same reason they keep close tabs on Jared Kushner, who I fully expect will be let go by Trump soon. There is too much liability with Kushner. Kushner has pressure from the Israeli lobby and Trump knows he is a delivery boy for AIPAC. The Israelis bugged Trump because they were concerned about Bannon, America First, the possibility that with a Trump win, they would see their foreign aid cut, which by the way, is going to happen.Q. What do you think of David Seaman? Is he a Mossad asset?A. Never heard of him.Q. How will this all play out?A. We are entering a time of political purge the likes of which has not been seen for decades, if not centuries. Trump has the evidence he needs to launch an investigation into a myriad of DC collusions. He must concentrate on the communications between Lynch, Bill Clinton, Obama, and Brennan. He needs to get serious with the pedophilia investigation because he can bring down his enemies in one fell swoop. McCain, Graham, Obama, Bill Clinton, and so on His greatest tools include the Wiener file titled Life Insurance. (Names, dates, photos, videos) and the Epstein videos captured by NSA when they were being delivered to Israeli intel, Wiener and Epstein. But, his greatest tool is the collective rage of the People. Trump must prosecute #PedoGate. The relationship between Schumer and Wiener must be explored. It may lead to some stunning climaxes, if you can excuse the pun.Q. This is huge!A. As I said before, there is enough underbelly rot to collapse not only our Government, but collapse the Likud part in Israel and expose a huge political pedophile ring that exists in the US, UK, Asia, etc. All inter-connected. And thats not even venturing into the extortion aspect.Q. Will it get bloody?A. Lets just say its flag weather.Q. Any advice for Trump?A He who hesitates is lost ..
SOURCE
- Home
- Forum
- Chat
- Donate
- What's New?
-
Site Links

-
Avalon Library

-
External Sites

- Solari Report | Catherine Austin Fitts
- The Wall Will Fall | Vanessa Beeley
- Unsafe Space | Keri Smith
- Giza Death Star | Joseph P. Farrell
- The Last American Vagabond
- Caitlin Johnstone
- John Pilger
- Voltaire Network
- Suspicious Observers
- Peak Prosperity | Chris Martenson
- Dark Journalist
- The Black Vault
- Global Research | Michael Chossudovsky
- Corbett Report
- Infowars
- Natural News
- Ice Age Farmer
- Dr. Joseph Mercola
- Childrens Health Defense
- Geoengineering Watch | Dane Wigington
- Truthstream Media
- Unlimited Hangout | Whitney Webb
- Wikileaks index
- Vaccine Impact
- Eva Bartlett (In Gaza blog)
- Scott Ritter
- Redacted (Natalie & Clayton Morris)
- Judging Freedom (Andrew Napolitano)
- Alexander Mercouris
- The Duran
- Simplicius The Thinker







 Reply With Quote
Reply With Quote




















Bookmarks